Know Your Customer (KYC) processes are essential for establishing trust and preventing fraud. But with the collection of sensitive personal data comes the responsibility to protect it. That’s why your IT service company plays a crucial role in enabling secure identity verification while maintaining data privacy.
Key Strategies for Your IT Service Company
- Data Minimization: Collect only the absolute minimum personal data necessary for KYC. Your systems should guide customers in providing the essential information.
- Access Controls: Strictly enforce access control protocols. Only authorized personnel should have access to sensitive KYC data, and their activities should be closely monitored.
- Transparency and Consent: Clearly communicate to customers why you’re collecting their data, how it will be used, and how it will be protected. Obtain explicit consent before proceeding with KYC.
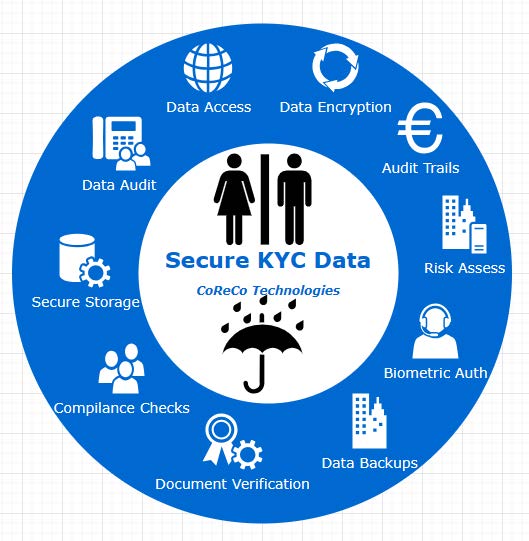
Technical Best Practices to Secure KYC Data
- Robust Encryption: Implement strong encryption for data in transit (HTTPS) and at rest (database encryption). Your IT expertise in selecting the right algorithms is key.
- Masking: When displaying KYC data, mask sensitive parts (e.g., only show the last few digits of identification numbers).
- Multi-Factor Authentication (MFA): Enforce MFA for all systems that handle KYC data, ensuring that a password alone isn’t enough for access.
- Secure Backups: Regularly back up KYC data, encrypting backups and storing them securely. Test your restoration procedures.
- Audit Trails: Maintain meticulous audit logs tracking every access to and modification of KYC data. Review these logs for suspicious activity.
- Data Residency: Ensure your systems are designed to comply with data residency laws in the regions you operate.
- Legal Compliance: Stay up-to-date on data protection regulations like GDPR, CCPA, etc., and be prepared to advise clients.
- Secure Disposal: When KYC data is no longer needed, destroy it irrecoverably using industry-standard deletion methods.
Additional Considerations: The Value of AI
Your IT company can further elevate its KYC offerings by integrating Artificial Intelligence (AI) solutions:
- Document Verification: AI algorithms excel at analyzing and verifying the authenticity of ID documents.
- Biometric Authentication: Facial recognition and other biometric technologies backed by AI offer secure identity confirmation.
- Risk Assessment: AI-powered risk models help your clients make informed decisions about user onboarding.
- Compliance: Automate compliance checks, ensuring your clients’ KYC processes align with regulations.
- Fraud Detection: Implement AI-driven fraud monitoring that continuously adapts to new threats.
For more details about such case studies, do visit us at www.corecotechnologies.com and to convert this virtual conversation into a real collaboration, please write to [email protected].
Sourabh
CoReCo Technologies



